PHISHING
Fraudulent communication from what initially appears to be a trustworthy source.
OVERVIEW
Watch out for fraudulent communications
With more staff working remotely, cyber criminals know that working from home makes businesses vulnerable as users spend more time online with fewer security systems in place and in some cases, using unprotected personal devices to access business resources.
Phishing is the most common and easiest form of cyberattack for criminals. It typically involves a user receiving fraudulent communication from what appears to be a trustworthy source, such as email, adverts or sites that you may frequently use.
A common example is email phishing, where hackers pretend to be organisations or people via email in order to steal sensitive information from your employees.
HOW DOES PHISHING WORK?
Below are two common examples of phishing;
Malicious Attachments
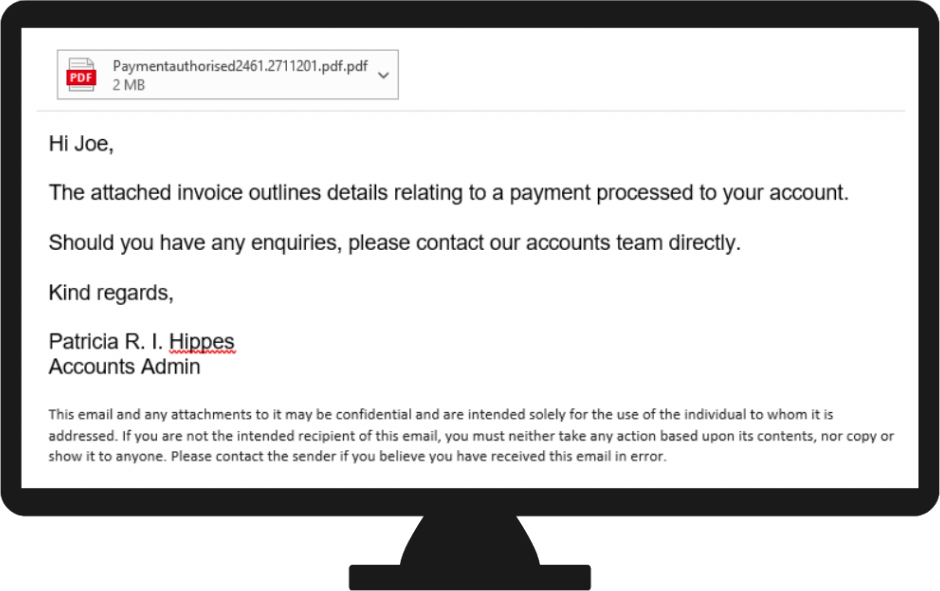
Malicious email attachments usually have enticing names, such as ‘Payment’ or ‘Invoice’ and once opened, malware is installed on the user’s machine.
Links to Malicious Websites
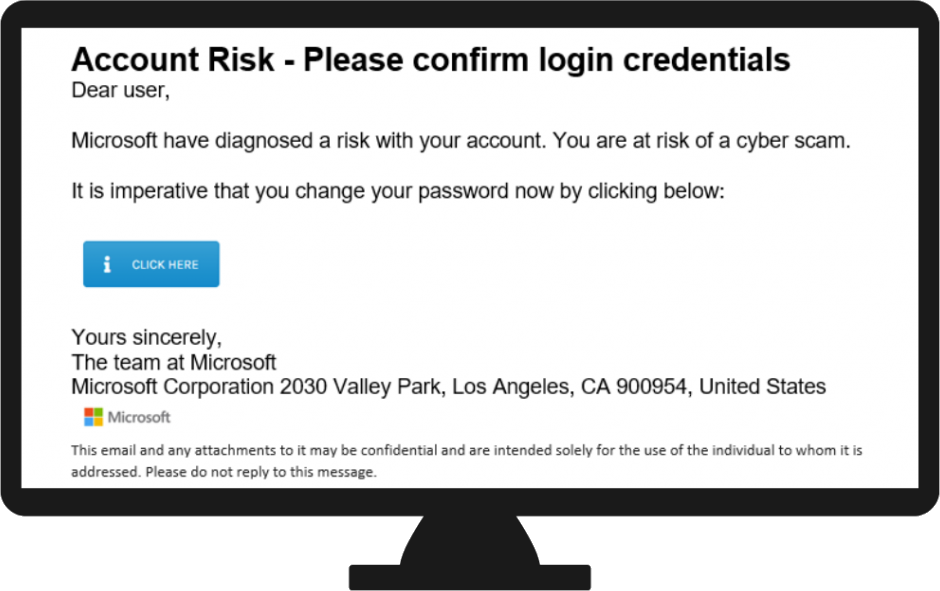
Malicious links direct to websites that are often clones of legitimate ones, which download malware once clicked on.
MORE THAN 80% OF ALL CYBER-INCIDENTS ARE CAUSED BY HUMAN ERROR
YOUR GREATEST DEFENCE
Your employees are your greatest defence against phishing. Knowledge and training on cyber safety is key to mitigate attacks.
Education on phishing awareness along with simulation training can significantly reduce the risk of an attack – because employees who can learn to recognise a phishing attempt can help stop the attack at source.

Phishing Simulations
Our email phishing simulations are more than just your normal phishing awareness training. A simulated phishing campaign tailored to your company allows you to not only test employees in the same setting as actual phishing emails, but it also allows you to provide training at the very moment an employee clicks on a suspicious connection, teaching them, there and then.
As part of user security awareness, regular phishing simulations enable employees to understand the dangers of social engineering, detect potential attacks, and take the appropriate reporting actions to protect the organisation.
We’ve partnered with Crest accredited IT Governance to deliver this service.

For more information, get in touch with us below
GET IN TOUCH WITH US
Get the help you need 24/7 - We’re here for you every step of the way
